European brand managers face a growing challenge in 2026. Counterfeiters deploy sophisticated methods to replicate products, damaging brand authenticity and consumer trust. Basic security measures no longer suffice. Advanced multi-layered holograms combined with tamper-evident labels and comprehensive compliance strategies offer proven protection. This guide walks you through a step-by-step approach to reduce counterfeit threats by up to 70% while meeting European regulatory standards.
Table of Contents
- Prerequisites: What You Need Before Starting
- Step 1: Conduct a Brand Security Risk Assessment
- Step 2: Design and Develop Customized Security Holograms
- Step 3: Combine Holograms with Tamper-Evident Labels
- Step 4: Train Supply Chain Stakeholders and Retailers
- Common Mistakes and How to Fix Them
- Expected Outcomes and Success Metrics
- Alternative Anti-Counterfeiting Approaches and Their Tradeoffs
- Protect Your Brand with Custom Security Holograms from Hologram4U
- FAQ
Key Takeaways
| Point | Details |
|---|---|
| Multi-layered holograms with tamper-evident labels reduce counterfeit sales by up to 70% within the first year. | |
| Comprehensive brand security risk assessment and regulatory compliance form the foundation for effective anti-counterfeiting. | |
| Training supply chain and retail stakeholders cuts authentication errors by over 50%, improving detection rates. | |
| Security features require updates every 12-18 months to stay ahead of evolving counterfeit tactics. | |
| Alternative technologies like RFID offer benefits but involve tradeoffs in cost, complexity, and consumer verification ease. |
Prerequisites: What You Need Before Starting
Before implementing advanced anti-counterfeiting measures, you need a solid foundation. Rushing into hologram deployment without proper preparation leads to gaps in protection and wasted resources.
Start with a thorough brand security needs assessment. Identify where your products are most vulnerable. Are counterfeiters targeting your packaging, labels, or distribution channels? Understanding these weak points shapes your security strategy.
Next, familiarize yourself with European regulatory frameworks. The EU Falsified Medicines Directive (FMD) sets strict standards for pharmaceutical products, but other industries have compliance requirements too. Regulations vary by product category and market, so consult legal advisors early.
Selecting the right security hologram provider matters enormously. Look for certified expertise and a proven track record in compliance. Custom security hologram providers should offer end-to-end services from design through manufacturing, ensuring your solutions meet regulatory standards.
Finally, develop training plans for your supply chain and retail staff. The most sophisticated holograms fail if people cannot authenticate them correctly. Plan sessions that cover:
- Visual verification techniques for holograms and tamper-evident features
- Authentication tool usage and troubleshooting procedures
- Reporting protocols for suspected counterfeit products
- Ongoing education as security features evolve
These prerequisites set you up for success, ensuring your anti-counterfeiting measures deliver measurable protection.
Step 1: Conduct a Brand Security Risk Assessment
Every brand faces unique counterfeit threats. Generic security solutions waste money and leave gaps. A targeted risk assessment reveals exactly where to focus your efforts.
Begin by analyzing counterfeit threat levels in your specific market sectors and geographic regions. Certain European countries see higher counterfeit activity depending on product type. Luxury goods face different risks than pharmaceuticals or electronics.
Inventory your product vulnerabilities systematically. Examine packaging design, label placement, distribution channels, and retail environments. Counterfeiters exploit the weakest link, so identify every potential entry point.
Engage legal and regulatory advisors during this phase. They ensure your assessment aligns with compliance requirements and helps you avoid costly mistakes. Their expertise also guides risk-based security feature prioritization, balancing protection levels against budget constraints.
Prioritize security features based on your risk profile. High-value products in regions with elevated counterfeit activity need the most robust protection. Lower-risk items can use simplified measures, optimizing your security expenditure.
Pro Tip: Document your assessment findings in a detailed report. This becomes your roadmap for security implementation and helps justify budget requests to stakeholders. Update it annually as threats evolve.
A thorough risk assessment transforms anti-counterfeiting from guesswork into strategic investment.
Step 2: Design and Develop Customized Security Holograms
Once you understand your risks, translate them into tailored holographic designs. Generic off-the-shelf holograms offer minimal protection. Customization of holograms using layered effects like microtext, color-shifting inks, and QR codes enhances security and compliance.
Incorporate multiple visual security effects to create layered authentication. Microtext prevents digital reproduction. Color-shifting inks change hue at different viewing angles, making replication expensive. Three-dimensional images add depth that counterfeiters struggle to duplicate. Combining these features exponentially increases security.
Embed smart features for rapid verification. QR codes enable instant authentication via smartphone, perfect for consumers and supply chain checkpoints. These codes can link to secure databases verifying product authenticity in seconds. Serial numbers provide unique identifiers for tracking and warranty validation.
Plan production timelines realistically. Custom hologram features and production timelines typically require 8 to 16 weeks from concept to delivery. Factor in design iterations, regulatory approvals, and manufacturing lead times. Rushing this phase compromises quality.
Coordinate approvals to meet European regulatory standards during the design phase. For pharmaceutical products, this includes FMD compliance. Other industries have their own requirements. Work closely with your hologram provider to embed compliant features from the start.
Pro Tip: Request physical samples before committing to full production. Test them in real-world conditions under various lighting and handling scenarios. This reveals potential issues before manufacturing thousands of units.
Customized holograms form the cornerstone of your anti-counterfeiting strategy, but they work best as part of a layered approach.
Step 3: Combine Holograms with Tamper-Evident Labels
Holograms verify authenticity at a glance, but tamper-evident labels add critical physical security. Together, they create a formidable barrier against product fraud and refilling schemes.

Apply tamper-evident label design and deployment in conjunction with your holographic security. These labels leave visible evidence when someone attempts removal. The "VOID" pattern or honeycomb destruction makes tampering obvious to consumers and inspectors.
Utilize multi-layer security to deter unauthorized opening and refilling. Counterfeiters often target premium products, emptying authentic packaging and filling it with inferior goods. Tamper-evident seals break this scheme by revealing any interference.
Continuously monitor post-deployment effectiveness and product tampering rates. Track incidents reported by consumers, retailers, and distributors. This data reveals whether your security measures deter tampering or need adjustment.
Adjust label design tailored to product type and packaging category. Bottles need different solutions than boxes or pouches. Consider:
- Adhesive strength for various surfaces and temperatures
- Label size and placement for optimal visibility
- Material durability against handling and environmental conditions
- Integration with existing packaging processes
Combining holograms with tamper-evident labels provides comprehensive protection that addresses both authentication and physical security concerns.
Step 4: Train Supply Chain Stakeholders and Retailers
Even the most sophisticated security features fail if people cannot use them correctly. Comprehensive training transforms your technology investment into actual protection.
Implement detailed training on authentication methods for all stakeholders. Supply chain personnel need different skills than retail staff. Warehouse workers focus on rapid verification during handling. Store employees help consumers understand authenticity features. Tailor your programs accordingly.
Training reduces authentication errors by over 50%, improving counterfeit detection rates significantly. This improvement directly impacts your brand protection effectiveness. Fewer missed counterfeits mean better consumer safety and brand reputation.
Use feedback channels to improve training and system use continuously. After initial rollout, survey participants about challenges they face. Common questions reveal gaps in your program. Update materials and conduct refresher sessions addressing these issues.
Educate on spotting counterfeit indicators beyond holograms and labels. Teach recognition of:
- Packaging quality differences and printing inconsistencies
- Weight and texture variations from authentic products
- Suspicious sourcing or pricing that suggests counterfeits
- Documentation discrepancies in shipping and invoicing
Pro Tip: Create quick reference cards with visual examples of authentic versus counterfeit features. Staff can keep these at workstations for instant consultation. Include images showing proper hologram viewing angles and tamper-evident label integrity.
Training programs for supply chain authentication require ongoing investment, but the return in reduced counterfeit penetration justifies the cost.
Common Mistakes and How to Fix Them
Even well-intentioned anti-counterfeiting efforts stumble on predictable pitfalls. Learning from others' mistakes saves time and money.
Avoid single-layer security mistakes that counterfeiters easily bypass. Relying solely on one technology creates a single point of failure. Combine visual holograms, tamper-evident seals, and smart verification features. Layered security forces counterfeiters to defeat multiple systems, making replication economically unfeasible.
Prevent inadequate training and poor technology integration errors. Purchasing sophisticated holograms means nothing if staff ignore them or use them incorrectly. Budget time and resources for comprehensive education. Test staff periodically to ensure retention.
Anticipate counterfeiters' evolving tactics every 12 to 18 months. What works today becomes obsolete as criminals adapt. They study your security measures and develop workarounds. Stay ahead by:
- Monitoring counterfeit market intelligence and enforcement reports
- Updating hologram designs with new security features periodically
- Adjusting tamper-evident labels based on attempted breach patterns
- Refreshing training to address new counterfeit techniques
Maintain agile upgrade plans to keep security features current and effective. Work with your hologram provider to schedule regular reviews. Plan budget cycles that accommodate periodic security enhancements rather than treating anti-counterfeiting as a one-time expense.
Addressing these common mistakes proactively keeps your brand protection strategy robust and responsive.
Expected Outcomes and Success Metrics
Measurable results justify anti-counterfeiting investments and guide continuous improvement. Clear benchmarks show whether your strategy works.
Integrated holographic and tamper-evident systems cut counterfeit sales by up to 70% in the first year, boost consumer trust, and reduce product tampering significantly. This reduction translates directly to revenue protection and brand reputation preservation.

Consumer trust rises via visible and verifiable product authentication. When customers easily confirm authenticity, purchase confidence increases. They become brand advocates, knowing you take their safety seriously. Survey your customer base pre and post implementation to quantify trust improvements.
Product tampering incidents decrease by 70% after label integration. This metric applies across industries from pharmaceuticals to electronics to luxury goods. Track reported tampering cases monthly. Compare periods before and after security deployment to document improvement.
Verification speeds improve to under 5 seconds with smart holograms. QR code scanning enables instant authentication without specialized equipment. This efficiency benefits supply chain operations, retail environments, and consumer experiences. Time studies at various checkpoints reveal operational gains.
| Metric | Baseline | After Implementation | Improvement |
|---|---|---|---|
| Counterfeit Sales Rate | 15% market share | 4.5% market share | 70% reduction |
| Consumer Trust Score | 62/100 | 84/100 | 35% increase |
| Tampering Incidents | 230/month | 69/month | 70% decrease |
| Authentication Time | 23 seconds | 4 seconds | 83% faster |
These outcomes demonstrate the tangible value of comprehensive anti-counterfeiting strategies.
Alternative Anti-Counterfeiting Approaches and Their Tradeoffs
Holograms excel at visual authentication, but other technologies offer different advantages. Understanding alternatives helps you make informed choices.
Holograms provide visual multi-layer security with easier consumer verification at moderate cost and less infrastructure. Consumers authenticate products instantly without special equipment. Implementation requires coordination with packaging suppliers but not extensive IT systems. Costs scale reasonably with production volumes.
RFID tags enable real-time product tracking with higher cost and complexity but enhanced logistics data. Radio frequency identification tracks items throughout supply chains, providing inventory visibility and anti-diversion intelligence. However, readers cost significantly more than visual inspection. Tags themselves run 10 to 50 times the price of holograms. Data management systems add ongoing expenses.
Evaluate specific brand needs around visual authenticity versus logistics tracking priorities. Luxury brands emphasizing consumer-facing authentication lean toward holograms. Pharmaceutical companies needing supply chain traceability often choose RFID despite higher costs. Many implement both technologies for different purposes.
Comparison of holograms and RFID solutions helps clarify which approach fits your situation:
| Feature | Security Holograms | RFID Tags |
|---|---|---|
| Consumer Verification | Easy visual inspection | Requires reader device |
| Implementation Cost | Moderate | High |
| Supply Chain Tracking | Limited | Comprehensive |
| Infrastructure Needs | Minimal | Extensive IT systems |
| Per-Unit Cost | Low to moderate | High |
| Regulatory Compliance | Excellent for visible authentication | Strong for traceability |
Select solutions aligning with budget, compliance, and product category requirements. Some brands use holograms for consumer-facing authentication and RFID for internal logistics, capturing benefits of both approaches.
Protect Your Brand with Custom Security Holograms from Hologram4U
You now understand how advanced holograms and tamper-evident labels cut counterfeit threats dramatically. Implementing these strategies requires a trusted partner with deep expertise.
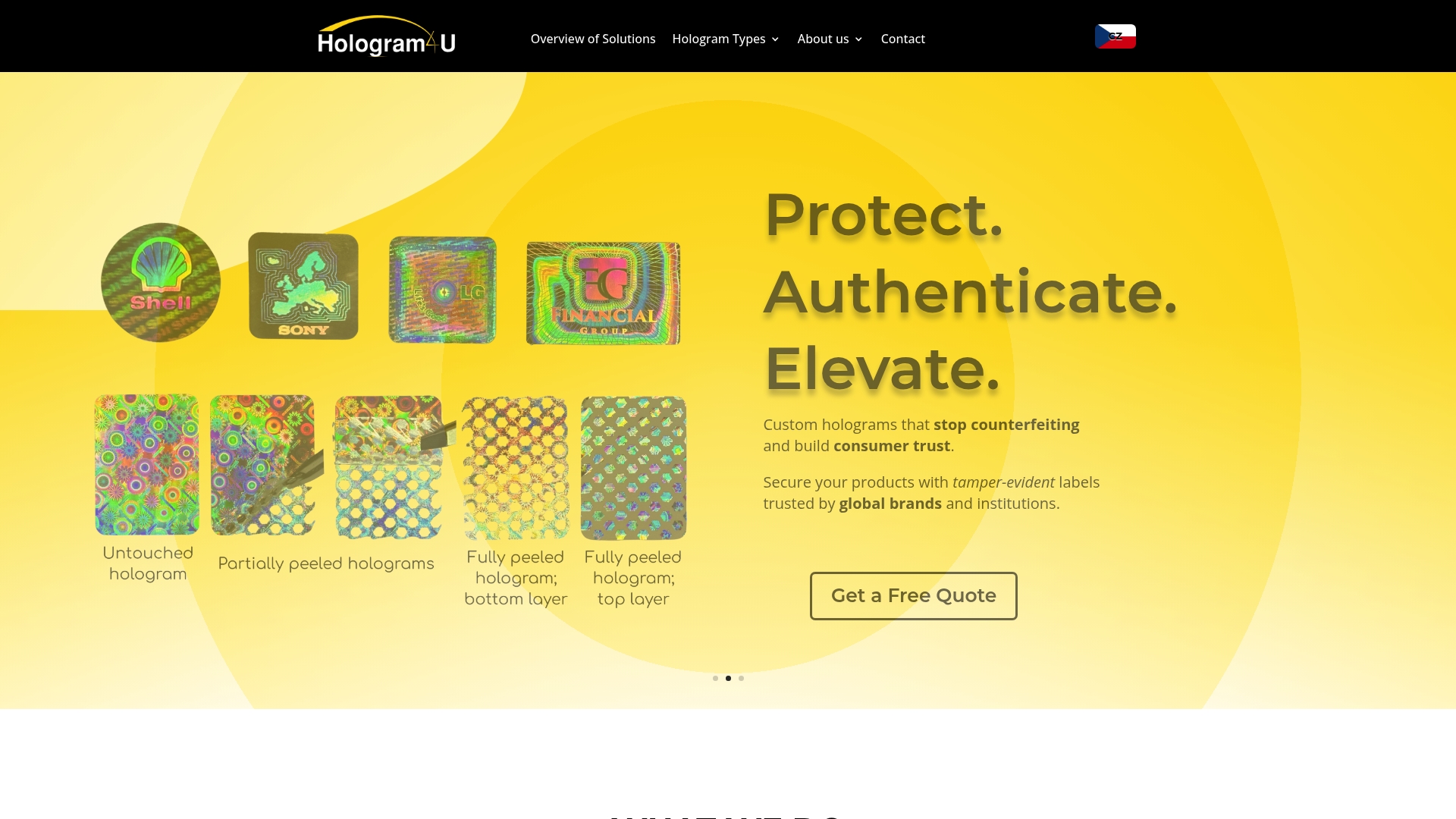
Hologram4U offers custom security holograms and tamper-evident labels backed by over 25 years of experience. Our custom hologram design solutions incorporate microtext, color-shifting inks, QR codes, and other advanced features meeting European regulatory compliance. We deliver end-to-end services from conceptual design through manufacturing and delivery.
Our solutions align with strict security and regulatory standards, ensuring your product integrity and brand authenticity. Trusted by leading brands including global corporations, government agencies, and financial institutions, we understand high-security applications across industries.
Act now to safeguard your brand against evolving counterfeit threats in 2026. Contact us to discuss your specific needs and receive a customized anti-counterfeiting strategy.
FAQ
What are the top anti-counterfeiting regulations brand managers must comply with in Europe?
The EU Falsified Medicines Directive (FMD) is the core regulation impacting pharmaceutical anti-counterfeiting, including hologram and serialization requirements. Other industries face sector-specific regulations depending on product category, such as electronics, luxury goods, and food safety standards. Consult legal advisors familiar with your specific market to ensure complete compliance.
How often should security hologram features be updated to stay effective?
Security features should be reviewed and updated approximately every 12 to 18 months to outpace counterfeiters' adaptations. Criminals study authentication methods and develop workarounds over time. Regular updates maintain security efficacy, regulatory compliance, and demonstrate your ongoing commitment to brand protection, deterring counterfeit attempts.
Can tamper-evident labels be used with any type of hologram design?
Tamper-evident labels are compatible with most hologram designs but should be tailored to your specific product and packaging. Proper integration maximizes security without compromising visual verification or production efficiency. Work with experienced providers to ensure tamper-evident labels compatibility with your holographic features and packaging materials.
What training methods work best for supply chain authentication?
Combine hands-on workshops with visual reference materials showing authentic versus counterfeit examples. Interactive sessions where staff practice authentication techniques under supervision build confidence and competence. Provide quick reference cards with images for on-the-job consultation. Follow up with periodic refresher training and testing to ensure retention as security features evolve.
How do smart holograms with QR codes improve verification speed?
QR codes embedded in holograms enable instant smartphone authentication, reducing verification time to under 5 seconds. Users scan the code to access secure databases confirming product authenticity without specialized equipment. This speed benefits supply chain checkpoints, retail environments, and consumer experiences while providing trackable verification data for analysis and reporting.
Recommended
- Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U | Securing Your Brand with Custom Holographic Seals & Labels
- Cookie Policy (EU) | Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U
- Promotional Hologram Stickers | Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U
- Custom Design | Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U