Counterfeiting threatens brand integrity across Europe, costing businesses billions annually. Combining holograms with tamper-evident labels reduces counterfeiting incidents by three times compared to single security methods. This guide walks you through proven anti-counterfeiting strategies, from advanced hologram customization to smart label integration, helping you select and deploy effective brand protection solutions that meet European regulatory standards while maximizing fraud prevention.
Table of Contents
- Key Selection Criteria For Brand Protection Solutions
- Advanced Hologram Customization Techniques
- Tamper-Evident Labeling Best Practices
- Integration Of Smart Features For Enhanced Authentication
- Comparison Between Anti-Counterfeiting Technologies
- Implementation And Deployment Tips For Brand Protection
- Summary Comparison And Situational Recommendations
- Secure Your Brand With Customized Holograms And Labels
- Brand Protection Tips FAQ
Key takeaways
| Point | Details |
|---|---|
| Hologram effectiveness | Multi-layer optical devices resist forgery 40% better than single-effect solutions. |
| Tamper evidence power | Tamper-evident labels provide visible proof in 95% of interference attempts. |
| Combined protection | Layering holograms with tamper-evident labels triples counterfeit risk reduction. |
| Smart authentication | QR codes and blockchain features enable instant verification and supply chain transparency. |
| Strategic balance | Effective protection requires aligning cost, compliance requirements, and technology integration. |
Key selection criteria for brand protection solutions
Selecting the right anti-counterfeiting strategy requires matching security features to your product risks and regulatory environment. European brands face unique compliance demands that influence technology choices.
Start by assessing the forgery resistance your product category demands. High-value goods like luxury watches or pharmaceuticals need multiple security layers, while everyday consumer products may require simpler solutions. Custom design security labels offer flexibility to match protection levels with threat profiles.
Evaluate these critical factors when choosing brand protection technology:
- Security feature complexity and visual distinctiveness that resist replication
- Compliance with EU anti-counterfeiting regulations and industry-specific standards
- Cost effectiveness relative to product value and counterfeit risk exposure
- Integration capability with existing packaging and smart authentication systems
- Customization flexibility to address unique product requirements and branding
Consider your supply chain complexity when selecting solutions. Products moving through multiple distribution points benefit from tamper-evident features that reveal unauthorized access. Manufacturing sectors with high counterfeiting rates, such as electronics or cosmetics, require robust verification methods that consumers can easily authenticate.
Pro Tip: Conduct a threat assessment before selecting security features. Map your distribution channels, identify vulnerability points, and choose technologies that address your specific weak spots rather than generic solutions.
Advanced hologram customization techniques
Modern hologram technology extends far beyond simple rainbow patterns. Holograms with multiple optical variable devices are 40% more resistant to forgery than single-effect versions, making them powerful weapons against sophisticated counterfeiters.
Multi-layer optical variable devices create complex visual effects that change based on viewing angle and lighting conditions. These sophisticated features combine depth perception, color shifts, and movement effects that are extremely difficult to replicate without specialized equipment. Custom security holograms incorporate these advanced elements to create unique brand identifiers.
Key hologram features that maximize protection include:
- Microtext elements visible only under magnification, adding a covert security layer
- Color-changing inks that shift hues under different lighting, providing instant visual verification
- Embedded QR codes linking to authentication databases for consumer verification
- 3D depth imagery creating visual movement that standard printing cannot reproduce
- Guilloche patterns with mathematical precision impossible to accurately copy
The forgery resistance comes from combining multiple authentication levels. Surface-level features deter casual counterfeiters, while covert elements like microtext enable expert verification. This layered approach means counterfeiters must overcome multiple technical barriers, dramatically increasing their cost and risk.
Smart integration amplifies hologram effectiveness. Embedding QR codes within holographic designs adds digital verification to physical security. Consumers scan the code to confirm authenticity while you gain supply chain visibility and customer engagement data.

Pro Tip: Request samples with your actual product packaging before committing to large orders. Test how holograms perform under your specific lighting conditions, handling requirements, and application surfaces to ensure optimal visibility and adhesion.
Tamper-evident labeling best practices
Tamper-evident labels provide immediate visual proof when someone attempts unauthorized product access. Over 95% of tampering attempts leave visible evidence when properly designed labels are used, making them essential for sectors requiring sealed integrity.
These labels work through destructive mechanisms that cannot be reversed without detection. When someone tries to remove or manipulate the label, it fractures, leaves residue, or reveals hidden warning text. This visible change alerts consumers and supply chain partners to potential compromise.
Implement these tamper-evident strategies for maximum protection:
- Void patterns that appear when labels are removed, making reuse impossible
- Fragile materials that shatter into pieces upon removal attempts
- Adhesive formulations that bond permanently, leaving residue on both surfaces
- Hidden messages revealed only when tampering occurs
- Serial numbers integrated with tracking systems for supply chain verification
Pharmaceuticals and food products benefit most from tamper-evident technology due to safety concerns and strict EU regulations. Luxury goods use these labels to protect high-value items during distribution. Electronics manufacturers apply them to warranty seals, deterring unauthorized repairs that could void coverage.
Combining tamper-evident labels with dual-image holograms creates layered security that addresses multiple threat vectors. The hologram prevents label replication while the tamper-evident feature reveals physical interference. This combination reduces counterfeit incidents by over 60% in targeted sectors.
Pro Tip: Position tamper-evident labels across package seams or closure points where access requires breaking the seal. This strategic placement ensures any opening attempt triggers visible evidence, unlike labels placed on flat surfaces that might be worked around.
Integration of smart features for enhanced authentication
Digital authentication features transform static labels into interactive brand protection tools. QR codes embedded in security labels enable instant mobile verification, connecting consumers directly to product databases while providing you with valuable tracking data.
Smart labels bridge physical and digital security layers. A consumer scans the QR code, receives immediate authenticity confirmation, and you capture location data, scan timestamps, and user information. This intelligence reveals distribution patterns and potential counterfeit hotspots.
Blockchain integration takes traceability further by creating immutable product history records. Each supply chain transaction gets recorded in distributed ledgers, making it impossible to alter product provenance. This transparency reduces supply chain losses by approximately 35% while building consumer trust through verifiable product journeys.
Key smart feature benefits include:
- Instant consumer verification through mobile scanning without expert knowledge
- Real-time supply chain visibility tracking products from manufacturing to sale
- Customer engagement opportunities through authentication interactions
- Data collection revealing counterfeiting patterns and distribution issues
- Integration with existing enterprise systems for seamless operations
Customizable holograms with embedded QR codes work particularly well for electronics, pharmaceuticals, and luxury goods where consumers expect digital interaction. The visible hologram provides immediate visual authentication while the QR code offers deeper verification for concerned buyers.
Smart features complement rather than replace physical security. Counterfeiters can copy QR codes, but they cannot replicate the secure database and blockchain records behind them. Combining both approaches creates comprehensive protection that addresses low-tech and sophisticated threats simultaneously.
Comparison between anti-counterfeiting technologies
Understanding how different technologies perform helps you allocate protection budgets effectively. Each approach offers distinct advantages depending on your product category, threat level, and operational constraints.
| Technology | Forgery Resistance | Cost Impact | Key Advantage | Primary Limitation |
|---|---|---|---|---|
| Multi-layer holograms | Very High | Moderate | Visual complexity deters casual counterfeiters | Requires consumer education for verification |
| Tamper-evident labels | High | 15-20% increase | Provides immediate visible evidence of interference | Cannot prevent initial counterfeiting |
| Smart QR codes | Moderate | Low to Moderate | Enables instant mobile verification and tracking | Vulnerable to code copying without backend security |
| Blockchain integration | Very High | High | Creates immutable product history records | Implementation complexity and infrastructure costs |
| Combined hologram + tamper | Exceptional | Moderate to High | Addresses multiple threat vectors simultaneously | Higher upfront investment required |
The data shows clear patterns for strategic deployment. Combining holograms with tamper-evident labels results in three times higher fraud reduction than single-method protections, justifying the additional investment for high-risk products.
Consider your threat landscape when selecting technologies. Luxury goods facing organized counterfeiting rings need the exceptional protection of combined hologram and tamper-evident solutions. Consumer electronics benefit from smart features that enable supply chain tracking. Pharmaceuticals require tamper evidence for regulatory compliance plus verification features for safety.
Budget constraints often drive decisions, but calculate total cost including counterfeit losses, brand damage, and regulatory fines. A multi-modal anti-counterfeiting study demonstrates that upfront security investments typically cost less than addressing counterfeit incidents after they occur.
Scale matters in technology selection. Large manufacturers can justify blockchain infrastructure costs through volume, while smaller brands should focus on cost-effective hologram and tamper-evident combinations that deliver strong protection without complex systems.
Implementation and deployment tips for brand protection
Successful brand protection requires more than selecting the right technology. Proper implementation determines whether security features deliver their full potential or create operational headaches.
Choose providers offering end-to-end services to reduce deployment errors by 30%. Fragmented vendors create integration challenges and finger-pointing when issues arise. Single-source providers handle design, manufacturing, and delivery while ensuring compatibility across your product line.
Follow these implementation steps for optimal results:
- Conduct product-specific threat assessments identifying vulnerability points in your supply chain
- Tailor label designs to match packaging materials, application methods, and handling conditions
- Verify EU anti-counterfeiting regulation compliance before committing to large production runs
- Test durability and tamper sensitivity on actual products under real-world conditions
- Train supply chain partners and consumers on authentication methods and security features
- Establish monitoring systems tracking security feature performance and counterfeit incidents
- Schedule regular security audits and feature updates addressing evolving counterfeiting tactics
Pilot programs minimize risk when deploying new security measures. Start with limited product lines or geographic regions, gather performance data, and refine your approach before full rollout. This staged deployment identifies issues while they are still manageable.
Custom design security labels allow iterative improvements based on field testing. You can adjust adhesive strength, visual elements, or smart features between production runs without abandoning your entire security strategy.
Maintain security through continuous improvement. Counterfeiters study your protection measures and develop workarounds over time. Regular feature updates and new authentication elements keep you ahead of evolving threats. Schedule annual security reviews examining counterfeit trends and updating defenses accordingly.
Summary comparison and situational recommendations
Strategic technology selection requires matching protection capabilities with your specific operational context. This comparison guides decision making across different industries and budget levels.
| Scenario | Recommended Solution | Primary Benefit | Investment Level |
|---|---|---|---|
| Luxury goods with high counterfeit risk | Combined hologram + tamper-evident | Maximum forgery resistance and visible interference evidence | High |
| Pharmaceuticals needing compliance | Tamper-evident with color-changing holograms | Regulatory compliance plus consumer verification | Moderate to High |
| Electronics requiring traceability | Smart labels with QR and blockchain | Real-time supply chain visibility and authentication | Moderate |
| Consumer goods with budget constraints | Stock holograms with basic tamper features | Cost-effective deterrence for casual counterfeiting | Low to Moderate |
| Multi-channel distribution | Hologram + QR code integration | Physical security plus digital tracking across channels | Moderate |
Luxury brands benefit most from layered protection combining multiple optical variable devices with destructive tamper evidence. The exceptional forgery resistance justifies higher costs when protecting premium products and brand reputation.
Pharmaceutical manufacturers must prioritize regulatory compliance alongside security. Color-changing inks provide consumer-friendly verification while tamper-evident features meet EU safety requirements. This combination addresses both legal obligations and brand protection simultaneously.
Electronics manufacturers should emphasize traceability through smart features. Supply chain complexity in this sector demands real-time visibility, making QR codes and blockchain integration valuable despite higher implementation costs.
Budget-conscious brands can still achieve meaningful protection through stock hologram designs customized with company branding. Basic tamper-evident features add security layers without requiring custom tooling or complex integration.
Scale your security investment with product value and risk exposure. High-margin products justify comprehensive protection, while volume goods need cost-effective solutions that maintain profitability. Review your protection strategy annually as your product mix and market threats evolve.
Secure your brand with customized holograms and labels
Protecting your brand requires expertise in both security technology and practical implementation. Hologram4U brings over 25 years of experience designing custom security holograms and tamper-evident labels that combine advanced features with operational practicality.
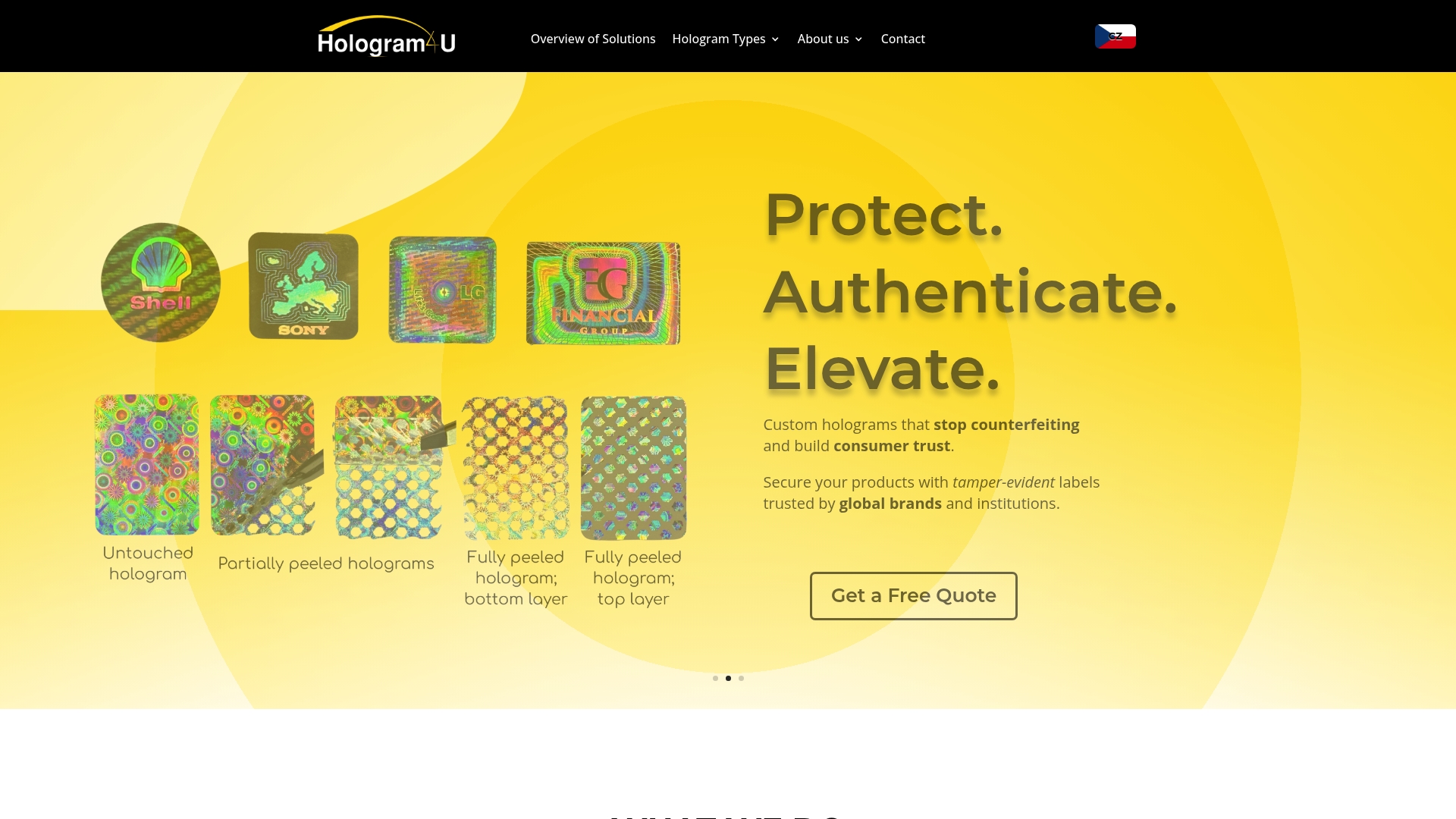
Our custom design security labels incorporate multi-layer optical devices, microtext, color-changing inks, and embedded QR codes tailored to your specific threats and compliance requirements. We handle end-to-end services from conceptual design through manufacturing and delivery, ensuring seamless integration with your existing operations.
Trusted brand protection partners across Europe rely on our certified holography expertise to combat counterfeiting in pharmaceuticals, luxury goods, electronics, and consumer products. Our solutions meet strict EU regulations while delivering the layered security that reduces fraud incidents by up to three times.
Brand protection tips FAQ
What are the advantages of combining holograms with tamper-evident labels?
Combining these technologies creates layered security addressing multiple threat vectors simultaneously. Holograms prevent label replication through complex optical effects while tamper-evident features reveal physical interference attempts. This combination reduces counterfeit incidents three times more effectively than single-method approaches, justifying the additional investment for high-value products facing sophisticated counterfeiting.
How do smart labels improve product authentication and traceability?
Smart labels with embedded QR codes enable instant consumer verification through mobile scanning while providing supply chain visibility. Each scan creates data revealing product location, authentication attempts, and distribution patterns. Blockchain integration adds immutable transaction records that make altering product provenance impossible, reducing supply chain losses by approximately 35% while building consumer trust.
Which brand protection solutions comply with European anti-counterfeiting regulations?
Tamper-evident labels with visible interference evidence meet EU safety requirements for pharmaceuticals and food products. Color-changing holograms provide consumer-friendly verification that satisfies regulatory authentication standards. Combined solutions addressing both physical security and traceability requirements ensure compliance across multiple EU directives while delivering comprehensive brand protection that withstands regulatory audits.
How can I test the effectiveness of security labels before full deployment?
Conduct pilot programs on limited product lines or geographic regions to gather real-world performance data. Test labels under actual handling conditions, lighting environments, and application surfaces that match your operations. Request samples applied to your packaging materials, then attempt removal and reapplication to verify tamper evidence appears as designed. Monitor initial deployment closely for adhesion issues, consumer feedback, and counterfeit detection rates before committing to large-scale rollout.
Recommended
- Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U | Securing Your Brand with Custom Holographic Seals & Labels
- Promotional Hologram Stickers | Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U
- Dual-Image Holograms | Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U
- Cookie Policy (EU) | Custom Security Holograms, Tamper-Evident Stickers & Labels with 20+ Years of Experience | Hologram4U